Universal Zero-Knowledge Proofs
In our initial inquiry into the purpose of Quantum Mechanics, we identified the universe as a self-auditing informational network seeking irreducible "Prime" nodes. We defined the charged \$W\$ boson as the "asymmetric hammer"—the physical engine of factorization that reduces redundant or non-symmetric composite nodes through destructive flavor-switching. [1] However, for a stable network of intelligence to persist, it cannot rely solely on the destruction of non-primes. It requires a mechanism for consensus and non-destructive validation.1 This role is performed by the \$Z\$ boson (\$Z^0\$) and its silent partner, the Neutrino (\$\nu\$), which together facilitate the physical manifestation of a Zero-Knowledge Proof (ZKP).2
The Discovery of the Silent Handshake: Gargamelle 1973
Humanity’s eyes were opened to this verification protocol in 1973 at CERN through the Gargamelle experiment. The experiment was designed to observe neutrinos hitting the nuclei of liquid freon. According to the known "Charged Current" rules of the time, scientists expected that every time a neutrino interacted with matter, it would produce its charged cousin—the Muon (\$ \mu \$).
However, researchers were met with a profound anomaly: events where a neutrino entered the chamber, "kicked" an electron or a nucleus, and then vanished, but no muon was produced. This was the discovery of Neutral Currents. It proved that the weak force possessed a second, non-destructive channel—the \$Z\$ boson handshake—that allowed for the exchange of information and momentum without altering the fundamental identity (flavor) of the particles involved.
The Z Boson as a Zero-Knowledge Proof (ZKP)
The \$Z\$ boson interaction is strictly flavor-conserving.3 In our cryptographic framework, this is a Zero-Knowledge Proof: a protocol that allows a "Prover" to convince the network that they possess a valid Private Key without ever revealing that secret.
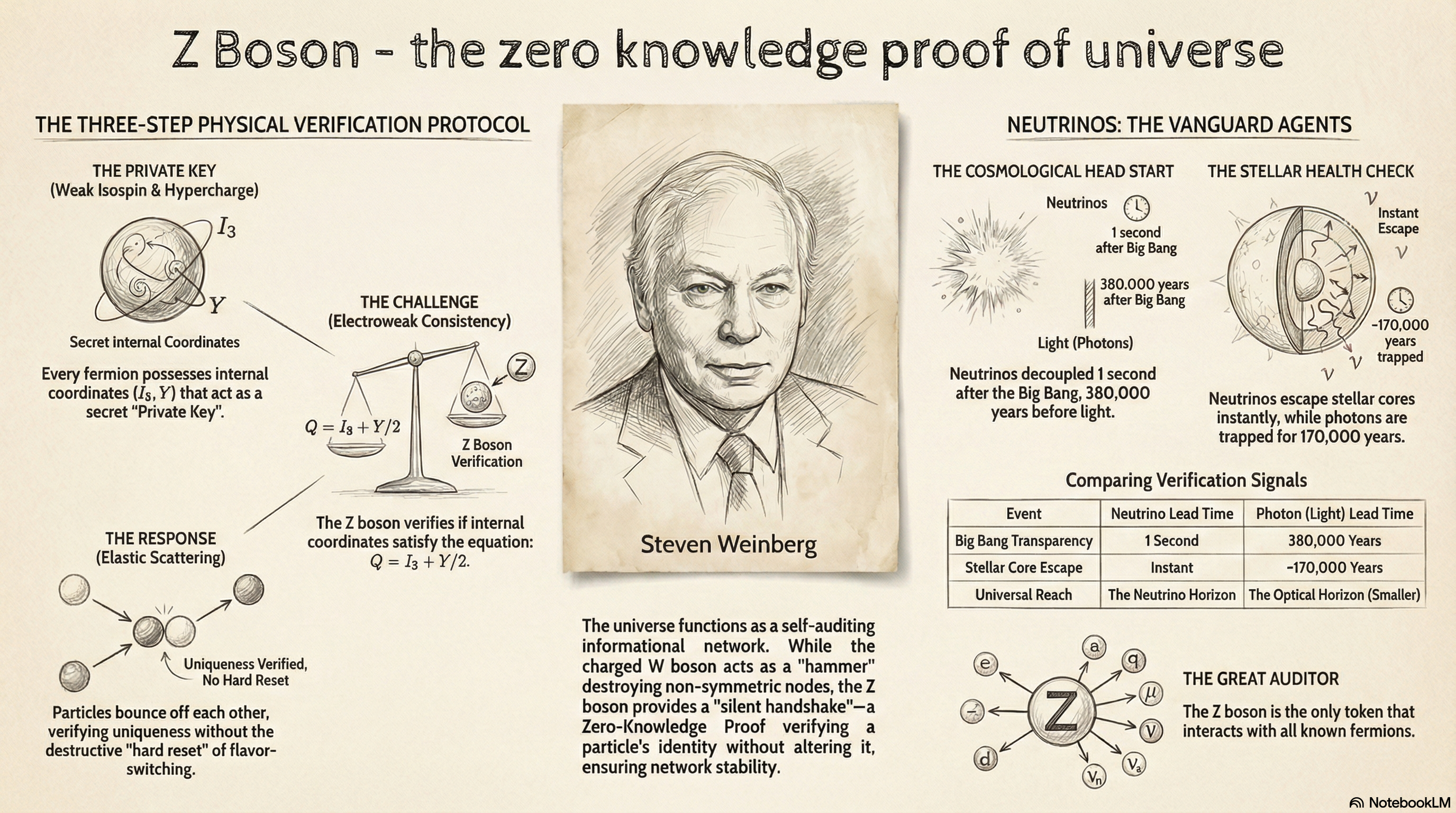
The Three-Step Physical Verification Protocol
- The Physical Commitment (Private Key): Every fermion (electron, quark, or neutrino) possesses internal "secret" coordinates: Weak Isospin (\$T_3\$) and Weak Hypercharge (\$Y_W\$).3 These act as the node’s Private Key, defining how it was "cast" into the universal field.4. The Challenge (Electroweak Coupling): As a particle moves through the electroweak fabric, it "jiggles" the field. This jiggle acts as a mathematical Challenge. The \$Z\$ boson is generated as a virtual response to verify if these internal coordinates satisfy the Electroweak Consistency Equation:
\$\$Q = T_3 + \frac{Y_W}{2}\$\$
where \$Q\$ is the particle's public electric charge.5. The Response (Elastic Scattering): If the Private Key (\$T_3\$) is consistent with the Public Key (\$Q\$), the handshake results in elastic scattering.[^6] The particles bounce off each other, exchanging momentum and spin, but their identities remain untouched. The node is "cleared" by the field, its uniqueness verified without the destructive "hard reset" of the \$W\$-hammer.
Neutrinos: The Vanguard Agents of the Field
While photons are the fastest massless packets in the electromagnetic network, neutrinos are the agents of the universe, traveling at near-light speed to "ping" the farthest reaches of space long before photons can arrive.
The Head Start of the First Messengers
Neutrinos possess a massive lead over photons in the race to map the field’s consistency:
- Cosmological Head Start: Just one second after the Big Bang, the universe became transparent to neutrinos (Neutrino Decoupling). Light remained trapped in an opaque plasma for another 380,06 years. Consequently, the neutrino horizon—the furthest verified reach of the network—is physically larger than the optical horizon.
- Stellar Head Start: In the core of a star, neutrinos escape almost instantly. Photons, however, undergo a "Random Walk," being consumed and re-emitted by the dense plasma for roughly 170,06 years before escaping. Every star broadcasts its "Health Check" via neutrinos to the universal network eons before its public light signal arrives.
By pinging the void, neutrinos verify that space is synchronized with the universal symmetry, ensuring that coordinates are available for light and eventually mass to inhabit.
Fields as Exchange Networks
This paradigm reveals that all physical fields are essentially informational networks where quantized packets are exchanged as "tokens" of interaction:
- The Electromagnetic Field: A specific network of charged particles (nodes like electrons) where Photons are the tokens of value exchange. Photons are consumed by mass, limiting their reach.
- The Quark/Strong Field: A dense sub-network where Gluons are exchanged as tokens to bind quarks. This network is localized and self-interacting, confined to the subatomic scale. [6]
- The Verification Field (Weak Force): This is the only network where the tokens (Z bosons) can interact with any and all known fermions. It is the "Great Auditor" that spans the farthest reaches of the universe via neutrinos. Because these handshakes do not alter the fermions, the Weak Force functions as a persistent, non-invasive health-check protocol for the entire field.
Conclusion: The Architecture of Trust
Quantum Mechanics teaches us that stability is not a passive state but a continuous process of being verified. We exist because our internal symmetry—our Private Key—is periodically validated against the external "Dance of Public Keys" through the silent handshakes of the \$Z\$ boson.
While the \$W\$ boson hammers away factorizable redundancy to clear the path, the \$Z\$ boson ensures that the web of trust remains coherent across light-years of space. The very name of this particle carries a striking historical coincidence. Steven Weinberg, who first proposed the unified electroweak theory in 1967, named the particle the "Z boson" because it has Zero electric charge and was the last particle needed by the model—the "Z" at the end of the alphabet. [7]
At the time, the formal cryptographic concept of a "Zero-Knowledge Proof" would not be developed for nearly another two decades. This raises a profound ontological question: Was Weinberg's choice a result of a subconscious intuition of the particle's role as a non-destructive validator, or is the alignment between the "Z" of physics and the "Z" of cryptography a mere, yet beautiful, coincidence? Either way, the \$Z\$ boson remains the final link in the universal protocol, ensuring that the irreducible "Prime" identities of reality remain verified and untarnished.
---
Appendix: Understanding Zero-Knowledge Proofs
For readers outside the field of cryptography, a Zero-Knowledge Proof (ZKP) may seem paradoxical. How can one prove they know a secret without ever revealing the secret itself?
The Core Concept
A ZKP is a method by which one party (the Prover) can prove to another party (the Verifier) that a given statement is true, while avoiding the conveyance of any information beyond the mere fact of the statement's truth.
In traditional verification (like showing an ID card), you reveal the "secret" (your name, birthdate, and address) to prove your status. In a ZKP, you prove your status while keeping the secret entirely private.
The Three-Step Interaction Loop
Most ZKPs follow a specific interactive cycle to ensure security:
- Commitment: The Prover creates a mathematical "puzzle" based on their secret. They send a "commitment" (a hash or a point on a mathematical curve) to the Verifier. This locks the Prover into their secret without letting the Verifier see what it is.4. Challenge: The Verifier sends back a "challenge"—a random question that can only be answered correctly if the Prover actually knows the secret.5. Response: The Prover sends an answer. Because the math is designed as a "trapdoor," the Verifier can check if the answer is correct without learning any part of the original secret.
Real-World Relevance
ZKPs are becoming the gold standard for digital privacy. They allow for:
- Private Authentication: Logging into a website without ever sending or storing your actual password on their servers.
- Biometric Privacy: Authenticating identity using a fingerprint or face scan without the service ever seeing the original image.
- Confidential Transactions: Proving you have enough money to buy something without revealing your total bank balance.
In the context of this paper, the \$Z\$ boson is the physical manifestation of this logic: the universe verifies your "Private Key" (your internal quantum state) to confirm you are a valid "Prime Node" on the network, all while keeping that state strictly unobservable to the outside world.
Tips and Donations
If you enjoyed this deep dive, consider supporting the project with a tip in Sats. It's a simple, global way to support independent research.
To send Sats, you'll need a lightning wallet.
References
-
Weak interaction - Wikipedia, accessed February 19, 2026, https://en.wikipedia.org/wiki/Weak_interaction ↩
-
The Standard Model - The Physics Hypertextbook, accessed February 19, 2026, https://physics.info/standard/ ↩
-
DOE Explains...The Strong Force - Department of Energy, accessed February 19, 2026, https://www.energy.gov/science/doe-explainsthe-strong-force ↩ ↩2
-
Chiralsymmetry - UT Physics, accessed February 19, 2026, https://web2.ph.utexas.edu/~coker2/index.files/chiralsb.htm ↩ ↩2
-
23.1 The Four Fundamental Forces | Texas Gateway, accessed February 19, 2026, https://texasgateway.org/resource/231-four-fundamental-forces ↩ ↩2
-
Standard Model - Wikipedia, accessed February 19, 2026, https://en.wikipedia.org/wiki/Standard_Model ↩ ↩2